The vulnerability management lifecycle is a continuous, structured process for identifying, evaluating, treating, and reporting on security vulnerabilities across your organization's IT assets. According to the 2025 Verizon Data Breach Investigations Report, 60% of breaches involved a known vulnerability for which a patch was available, making effective vulnerability management one of the most impactful security investments an organization can make. The average cost of a breach involving unpatched vulnerabilities was 21% higher than other breach types according to IBM's 2024 Cost of a Data Breach Report. This guide breaks down the six essential phases and the metrics that drive a mature program.
Key Takeaways
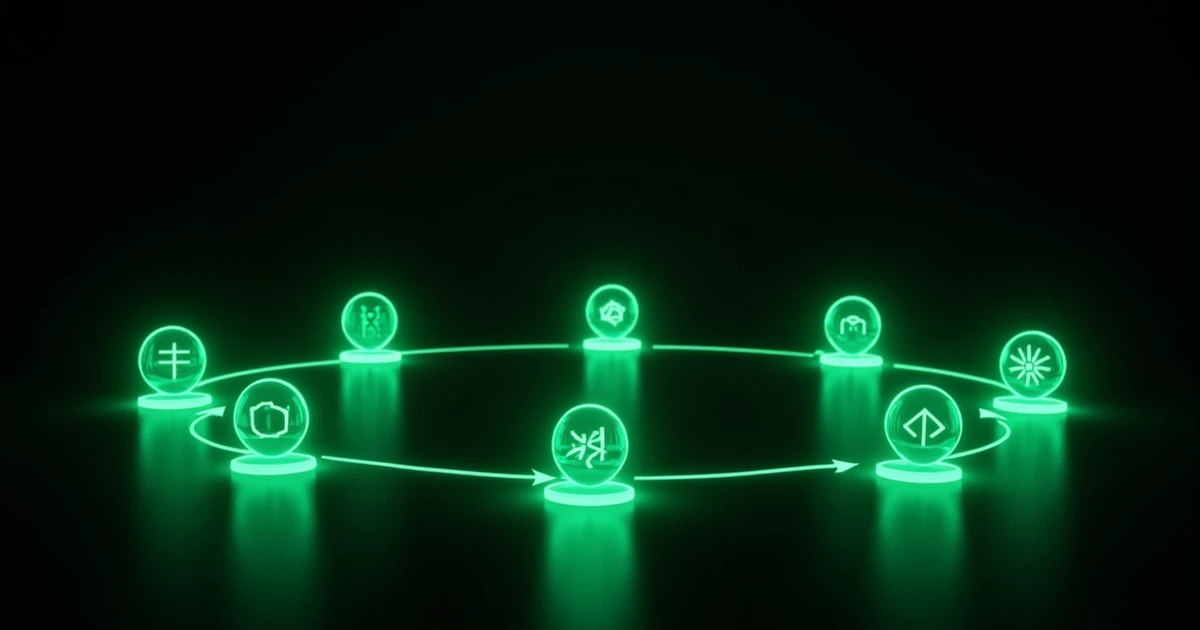
- Vulnerability management follows 6 phases: Discover, Prioritize, Assess, Report, Remediate, Verify
- CVSS scores alone are insufficient -- risk-based prioritization considers exploitability and business context
- Only 2-5% of vulnerabilities are actively exploited; focus resources on these
- Set SLA targets: Critical within 48 hours, High within 7 days, Medium within 30 days
- Automation reduces mean time to remediate by 60% (Forrester, 2024)
Phase 1: Discover
Discovery is the foundation of vulnerability management. You cannot fix what you cannot see. This phase involves two parallel activities: asset discovery (identifying all systems in your environment) and vulnerability scanning (detecting weaknesses in those systems).
NIST published over 29,000 new CVEs in 2024 alone, making continuous discovery essential. Key discovery methods include:
- Authenticated scanning: Agents or credential-based scans that provide deep visibility into installed software, configurations, and missing patches. Tools include Nessus, Qualys VMDR, and Rapid7 InsightVM
- Unauthenticated scanning: Network-based scans that identify externally visible vulnerabilities without credentials. Useful for external attack surface assessment
- Agent-based scanning: Lightweight agents installed on endpoints provide continuous vulnerability data, even for remote and mobile devices
- External attack surface management: EASM platforms like Orizon RECON discover internet-facing assets and their vulnerabilities from an attacker's perspective
- Application security testing: SAST, DAST, and SCA tools identify vulnerabilities in custom code and third-party dependencies
Discovery Best Practices
- Scan your entire environment at least weekly, with daily scans for critical systems
- Maintain a current and complete asset inventory as the basis for scanning scope
- Use multiple scan types (authenticated, unauthenticated, agent-based) for comprehensive coverage
- Include cloud workloads, containers, and serverless functions in your scanning scope
Phase 2: Prioritize
Not all vulnerabilities are equal. With tens of thousands of CVEs published annually, organizations must focus remediation resources on the vulnerabilities that pose the greatest risk to their specific environment. Research by Kenna Security (now Cisco) found that only 2-5% of published vulnerabilities are ever exploited in the wild, yet these few account for the vast majority of breach-enabling vulnerabilities.
Understanding CVSS Scoring
The Common Vulnerability Scoring System (CVSS) provides a standardized severity rating from 0.0 to 10.0:
| CVSS Score | Severity | Description |
|---|---|---|
| 9.0 - 10.0 | Critical | Easily exploitable with severe impact; often remotely exploitable without authentication |
| 7.0 - 8.9 | High | Significant impact; may require some conditions for exploitation |
| 4.0 - 6.9 | Medium | Moderate impact; exploitation typically requires local access or user interaction |
| 0.1 - 3.9 | Low | Limited impact; difficult to exploit in practice |
Beyond CVSS: Risk-Based Prioritization
CVSS base scores measure theoretical severity but not real-world risk. A CVSS 9.8 vulnerability in an isolated test system poses less risk than a CVSS 7.0 vulnerability in a public-facing payment application. Effective prioritization considers:
- Exploitability: Is there a known exploit? Is it in the CISA Known Exploited Vulnerabilities (KEV) catalog? Is it being actively exploited?
- Asset criticality: What is the business value and data sensitivity of the affected system?
- Exposure: Is the vulnerable system internet-facing, internal-only, or segmented?
- Compensating controls: Do existing defenses (WAF, IPS, segmentation) mitigate the vulnerability?
- EPSS score: The Exploit Prediction Scoring System provides a probability (0-1) that a vulnerability will be exploited in the next 30 days
Phase 3: Assess
Assessment goes beyond scanning to understand the real-world impact of discovered vulnerabilities. This phase involves validating findings, eliminating false positives, and determining the business context of each vulnerability.
- Validate findings: Confirm that reported vulnerabilities are genuine, not false positives from outdated scan signatures
- Assess business impact: Determine what an attacker could achieve by exploiting the vulnerability in your specific environment
- Identify dependencies: Map relationships between vulnerable systems and critical business processes
- Evaluate remediation options: Determine whether patching, configuration changes, compensating controls, or risk acceptance is most appropriate
- Estimate remediation effort: Factor in testing requirements, change windows, and potential service disruption
Phase 4: Report
Effective reporting translates technical findings into actionable intelligence for different stakeholders. Reports should be tailored to their audience:
- Executive dashboards: High-level risk posture, trend lines, compliance status, and comparison to industry benchmarks
- Technical reports: Detailed vulnerability data, affected systems, CVSS scores, exploit availability, and specific remediation steps
- Compliance reports: Mapping of findings to regulatory requirements (NIS2, PCI DSS, ISO 27001)
- Operational reports: SLA compliance, remediation velocity, open vulnerability aging, and team performance metrics
Key Metrics to Report
| Metric | Description | Target |
|---|---|---|
| Mean Time to Remediate (MTTR) | Average days from discovery to fix | Critical: <2 days, High: <7 days |
| Scan Coverage | % of assets regularly scanned | >95% |
| Vulnerability Density | Vulnerabilities per asset | Decreasing trend |
| SLA Compliance | % of vulns fixed within SLA | >90% |
| Reopen Rate | % of vulns that reappear after fix | <5% |
| Risk Score Trend | Overall risk score over time | Decreasing trend |
Phase 5: Remediate
Remediation is where vulnerability management delivers its value. The goal is to eliminate or mitigate vulnerabilities within defined SLA timeframes while minimizing operational disruption.
SLA Targets by Severity
| Severity | CVSS Range | Remediation SLA | Notes |
|---|---|---|---|
| Critical | 9.0 - 10.0 | 48 hours | Emergency patching; CISA KEV vulns require even faster response |
| High | 7.0 - 8.9 | 7 days | Priority scheduling; may require out-of-cycle maintenance windows |
| Medium | 4.0 - 6.9 | 30 days | Standard patch cycle; align with regular maintenance windows |
| Low | 0.1 - 3.9 | 90 days | Address during regular maintenance; consider risk acceptance for lowest-risk findings |
Remediation Options
- Patching: Apply vendor-provided patches. The preferred solution when available and tested
- Configuration changes: Harden settings, disable unnecessary features, or modify access controls
- Compensating controls: When patching is not immediately possible, implement WAF rules, network segmentation, or enhanced monitoring
- Virtual patching: Use IPS/WAF signatures to block exploitation while awaiting a permanent fix
- Risk acceptance: For low-risk findings where the cost of remediation exceeds the risk, document the decision and set a review date
Phase 6: Verify
Verification closes the loop by confirming that remediation was effective and has not introduced new issues. This phase is often overlooked but is critical for program integrity.
- Re-scan: Run targeted scans against remediated systems to confirm the vulnerability is resolved
- Regression testing: Verify that patches have not broken application functionality
- Penetration testing: Periodic pentests validate that remediated vulnerabilities cannot be exploited through alternative attack paths
- Control validation: If compensating controls were applied instead of patches, verify their effectiveness through testing
- Documentation: Update remediation records, close tickets, and capture lessons learned
Tools and Automation
Automation is essential for scaling vulnerability management. Forrester Research found that organizations using automated vulnerability management tools reduce their mean time to remediate by 60% compared to manual processes.
Key tool categories:
- Vulnerability scanners: Nessus, Qualys VMDR, Rapid7 InsightVM, OpenVAS
- EASM platforms: Orizon RECON, CyCognito, Censys
- Patch management: WSUS, SCCM, Intune, Automox
- Prioritization engines: Kenna.VM (Cisco), EPSS integration, Vulcan Cyber
- SOAR/ticketing: Jira, ServiceNow, Splunk SOAR for workflow automation
- Application security: Snyk, Checkmarx, Veracode for code-level vulnerability management
Building a Mature Program
Vulnerability management maturity progresses through four stages:
- Reactive: Ad hoc scanning, manual processes, no defined SLAs. Most organizations start here
- Defined: Regular scanning schedule, documented processes, basic SLAs, manual remediation tracking
- Managed: Risk-based prioritization, automated workflows, integration with CMDB and ticketing, measurable SLA compliance
- Optimized: Continuous scanning, predictive analytics, fully automated remediation for low-risk items, business-aligned risk reporting, continuous improvement cycle
Orizon's RECON and RECON Internal platforms support the full vulnerability management lifecycle, from external and internal discovery through prioritization, reporting, and remediation tracking. They help organizations progress from reactive scanning to a mature, risk-based program.
Summary
Effective vulnerability management is not about finding every vulnerability -- it is about finding the right vulnerabilities, fixing them quickly, and proving that they stay fixed. The six-phase lifecycle provides a structured approach that scales with your organization. Start by ensuring comprehensive discovery, implement risk-based prioritization to focus your resources, set and track SLA targets, and continuously verify that remediation is effective. The organizations with the strongest security postures are those that treat vulnerability management as a continuous operational discipline, not a periodic checkbox exercise.